Is DERO Lying About Having Achieved Fully Homomorphic Encryption?
DERO claims to have achieved Fully Homomorphic Encryption but it's not possible without multiplication operations and without adequate proof.
START UPDATE:
Since this post was written, DERO Foundation members have come to insist that the proof of concept code (DHEBP) does not need to demonstrate Fully Homomorphic Encryption or to wait for further development. Yet, every official announcement including the cover description for DHEBP states that it proves that they have achieved Fully Homomorphic Encryption.
At this time, no substantial arguments or evidence have been brought to counter my criticisms except for simple deflections. I further provide the responses from DERO Foundation and a few longstanding DCAB members below:
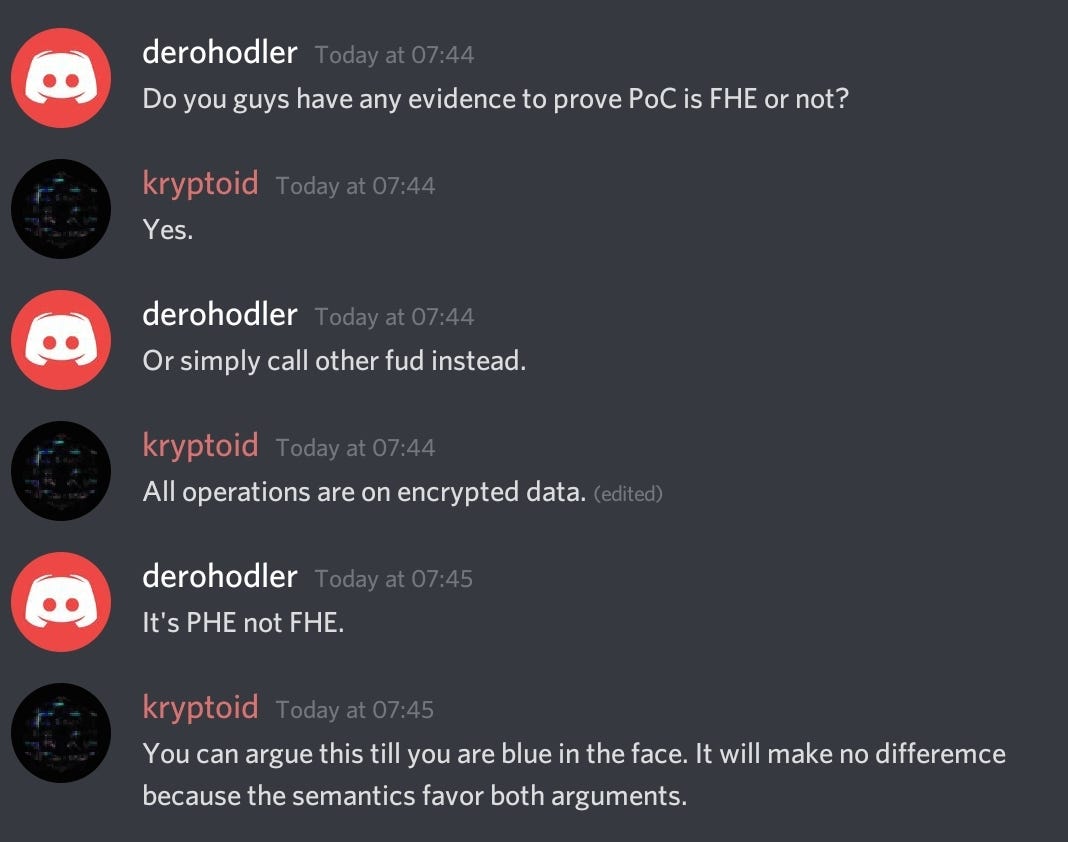
DERO Responses to FHE claim
DERO Foundation CEO claims that the DHEBP does not require proving FHE since “multiplication is not required”. Yet the DHEBP is supposed to prove FHE transactions
DERO Foundation CTO making an incredilous claim that it is Fully Homomorphic Encryption simply because “all operations are on encrypted data”. This is shocking since it reveals a lack of knowledge in cryptographic standards.
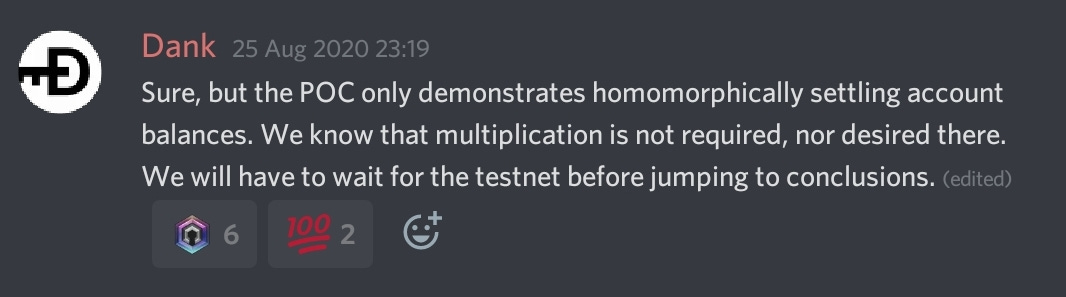
A longstanding DCAB member admitting that FHE is not present, but to wait and see…
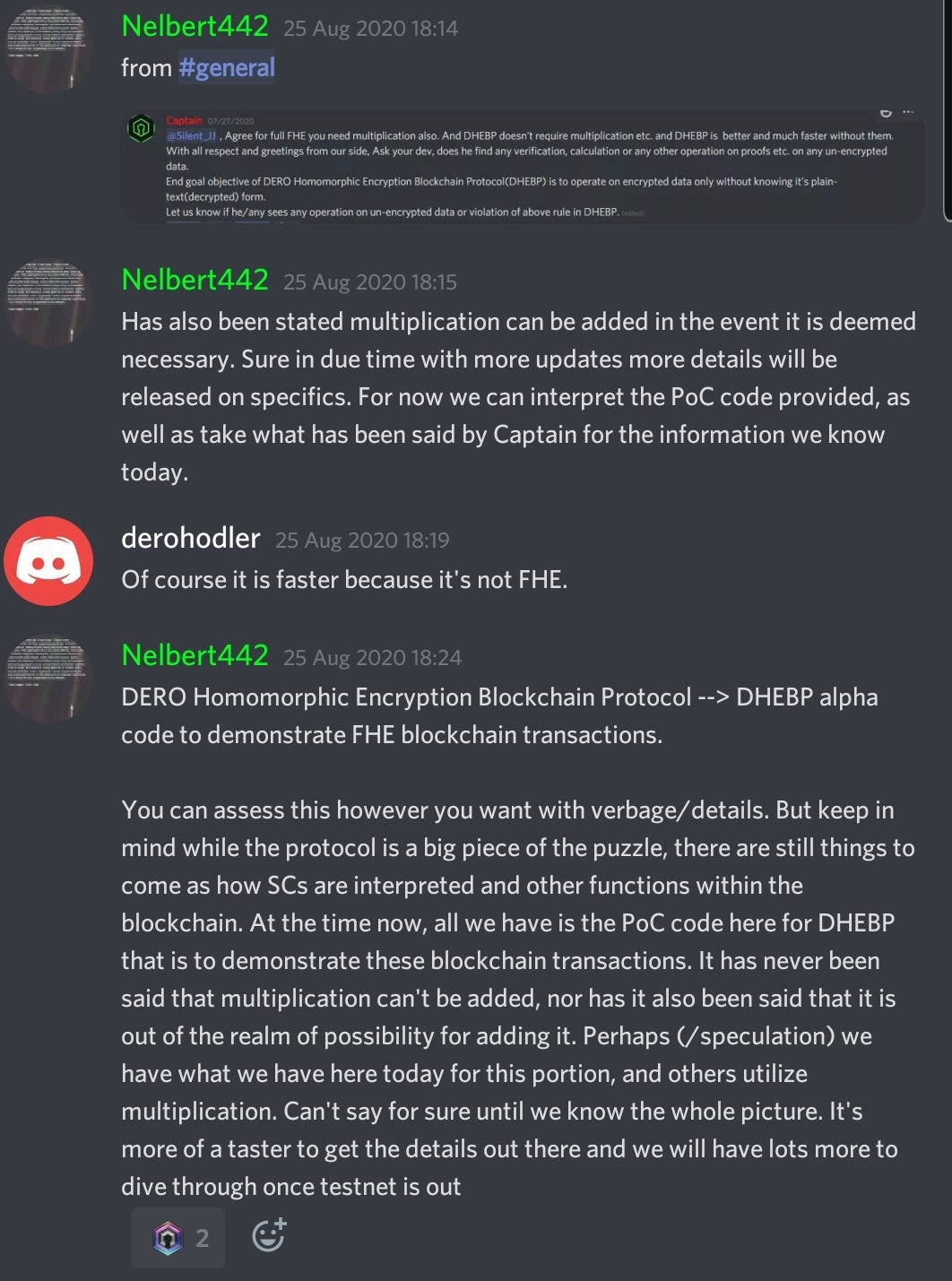


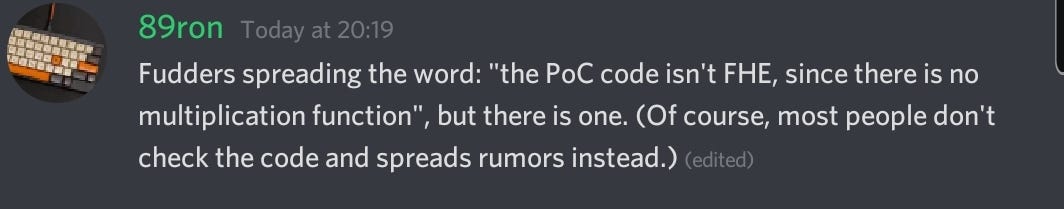
A longstanding DCAB member claiming that an arithmetic function used to support Pederson’s Commitment Scheme (not FHE) in order to rebuke my criticisms as baseless.


END UPDATE

One of the most exciting and ground breaking news about the DERO project is that they claim to have achieved Fully Homomorphic Encryption (FHE). Their recent proof of concept code release supposedly backs their claim.
What makes Fully Homomorphic Encryption full?
tl;dr: FHE means it can run both add and multiply operations
To understand whether DERO has achieved FHE or not, it’s important to know that there are three types of homomorphic encryption:
Partially Homomorphic Encryption (PHE)
Somewhat Homomorphic Encryption (SHE)
Fully Homomorphic Encryption (FHE)
FHE is considered the holy grail of security because it is capable of any number of addition and multiplication computations on your ciphertext (the result of encryption on your plaintext), thus making it very secure. However, because of how computationally intensive FHE is — it is widely considered impractical until recently with new advances in efficient schemes and technology by IBM, Microsoft and other developments.
PHE allows only either addition or multiplication to be performed on the ciphertext. This makes it very efficient and is already commonly used in security. It should be noted that PHE with multiplicative operations is the foundation for RSA encryption, which is commonly used in establishing secure connections through SSL/TLS.
SHE is one that supports select operation (either addition or multiplication) up to a certain complexity, but these operations can only be performed a set number of times.
DERO advertises its FHE claim everywhere, literally
So it must be 100% the truth! It’s shown on their website:
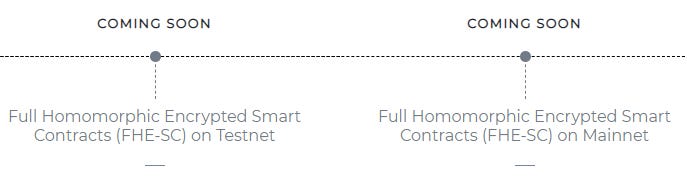
Their June monthly update:

Their July monthly update:
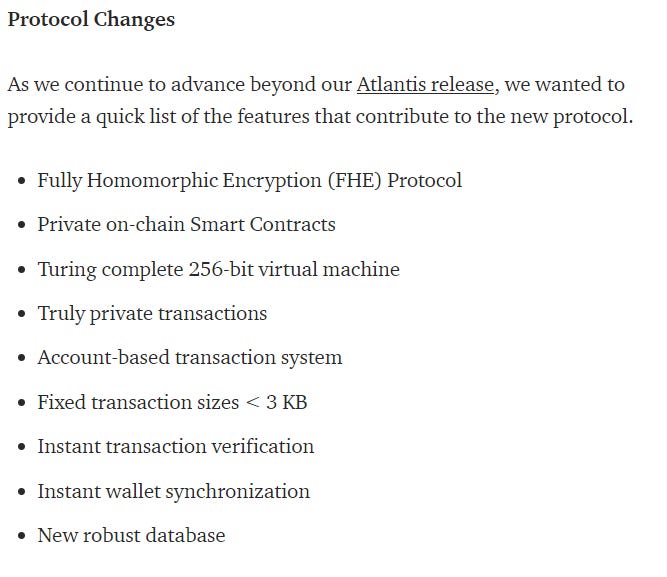
Their proof of concept code release:
And pretty much all of their tweets:
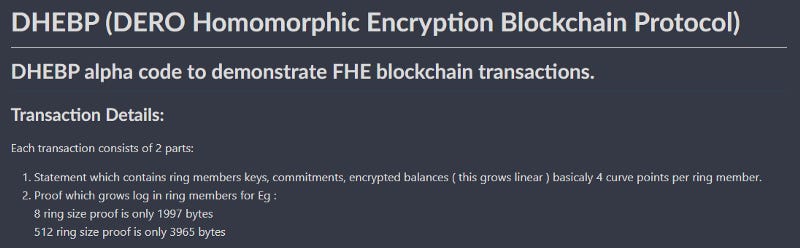
One DERO community member was diligent enough to ask the team from NuCypher (who is working on GPU-optimized FHE) about the code. And their response was that it isn’t FHE.
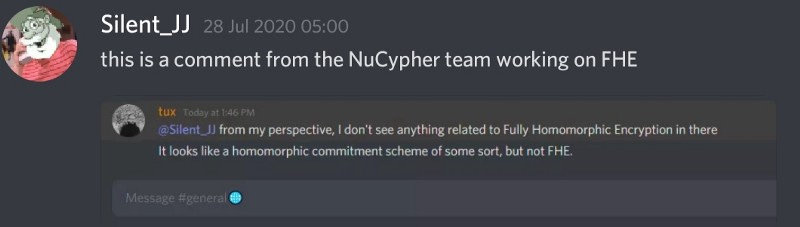
The NuCypher comment isn’t wrong to say that it looks like a homomorphic commitment scheme. Pederson’s commitment scheme is used in Monero, and it’s one of the features present in DERO codebase, as shown in their wiki:
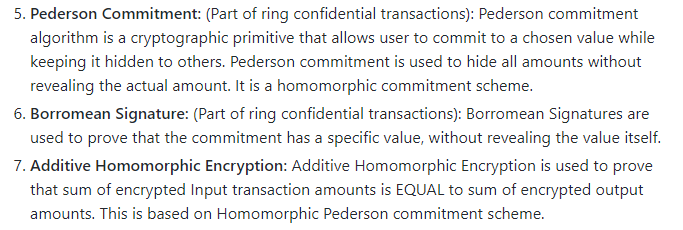
What’s interesting is that NuCypher says that the DHEBP doesn’t prove FHE, and the wiki image of features only lists Additive Homomorphic Encryption. This is further supported by the DERO developer’s own comment:
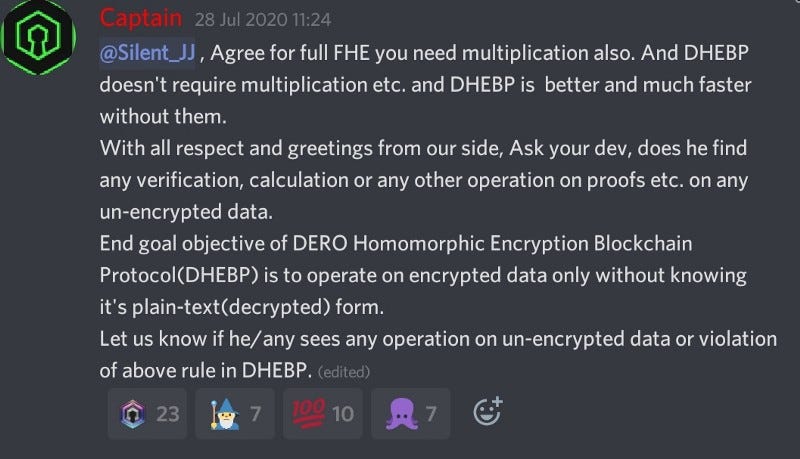
The DERO developer acknowledges that full FHE can only be achieved if it can run multiplication operations, and removed multiplication operations for the sake of efficiency. The comment, in addition to the wiki list of features and the external review of the DHEBP is a clear admission that the proof of concept that supposedly claims to be FHE is infact only PHE.
So what do we know so far?
DERO developers are aware that their implementation is not FHE;
DERO developers continue to mention FHE in official materials;
DERO foundation heavily advertises “FHE as being achieved”; and
There is no mention of PHE being the actual implementation anywhere.
It seems that both the developers and foundation members are complicit in misleading the public that it has achieved FHE when in fact, it has only implemented PHE. Confusingly, it seems that DERO developers knew that they were going to pursue PHE all along. The github wiki was updated in December 2019 to add Additive Homomorphic Encryption to the list of technologies used.
Why they chose to be dishonest and claim FHE was achieved when PHE is a perfectly efficient technology to apply and has already been used heavily in cryptography is curious.
In choosing to be dishonest and misleading, it risks being labeled a scam, again.
Perhaps, the DERO developers have an explanation for why they are claiming to have achieved FHE in their new protocol inspite of having only addition operations. The burden of proof is on them to prove it through paper and explanation, which is the academic standard and norm. The explanation and the math supporting the code are as yet absent. Until these are adequately provided, it would be an argument based on ignorance to say that the burden of proof lies on the counter-party to prove DERO wrong.